monogramm / mautic-ldapauth-bundle
This plugin enables LDAP authentication for mautic.
Package info
github.com/Monogramm/MauticLdapAuthBundle
Type:mautic-plugin
pkg:composer/monogramm/mautic-ldapauth-bundle
Requires
- php: >=5.6.19 <7.3
- mautic/composer-plugin: ^1.0
- symfony/form: ~2.8
- symfony/http-foundation: ~2.8
- symfony/ldap: ~2.8
- symfony/security: ~2.8
- symfony/translation: ~2.8
Requires (Dev)
- leanphp/phpspec-code-coverage: ~2.1
- phpspec/phpspec: ~2.1
- squizlabs/php_codesniffer: ~3.0
This package is auto-updated.
Last update: 2022-09-04 17:42:02 UTC
README
Mautic LDAP Authentication Plugin
This Plugin enables LDAP authentication for mautic 2 and newer. Even though Mautic offers SAML authentication, the main objective is to offer an alternative to those who do not want to setup SSO in their company just for mautic 😃
Installation via composer (preferred)
Execute composer require monogramm/mautic-ldap-auth-bundle in the main directory of the mautic installation.
Installation via .zip
- Download the master.zip, extract it into the
plugins/directory and rename the new directory toMauticLdapAuthBundle. - Install
symfony/ldaprequirements with composer:composer require symfony/ldap:~2.8 - Clear the cache via console command
php app/console cache:clear --env=prod(might take a while) OR manually delete theapp/cache/proddirectory.
Configuration
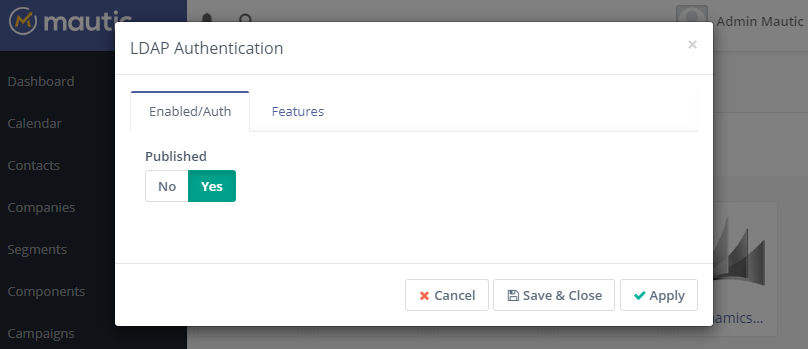
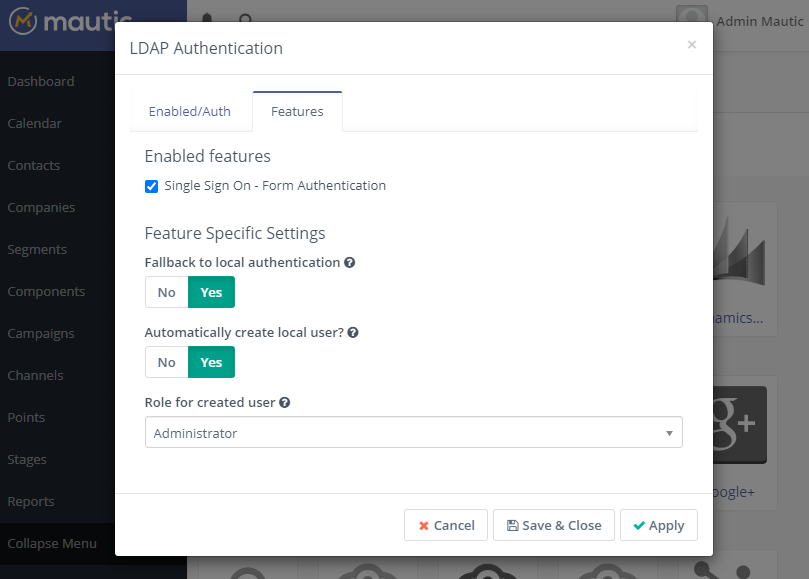
Navigate to the Plugins page and click "Install/Upgrade Plugins". You should now see a "LDAP Auth" plugin.
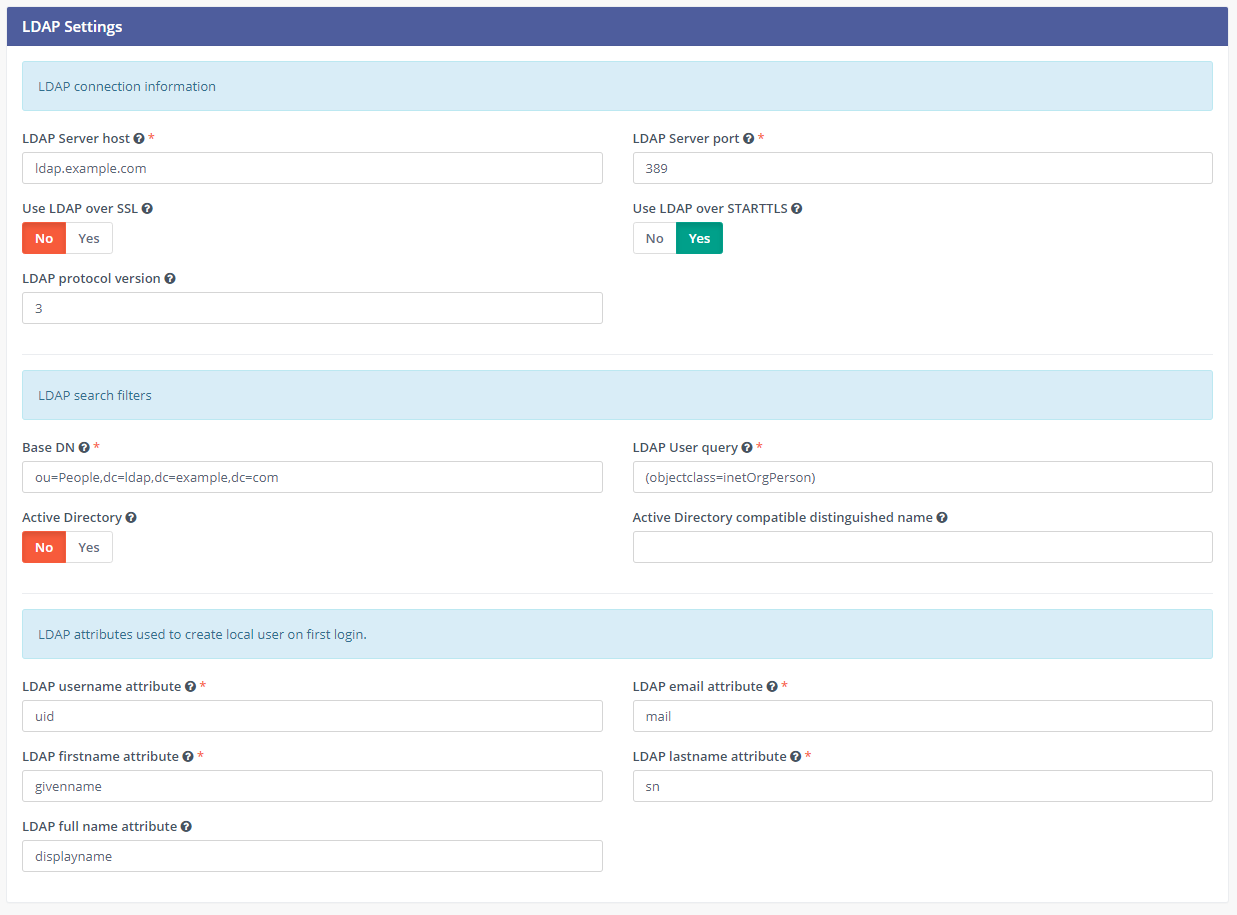
After activating the plugin, you can now go to "Configuration > LDAP Settings" to edit the parameters:
You can also edit manually your parameters in local.php (adapt to your LDAP configuration):
//'parameters' => array( // ... 'ldap_auth_host' => 'ldap.mysupercompany.com', 'ldap_auth_port' => 389, 'ldap_auth_version' => 3, 'ldap_auth_ssl' => false, 'ldap_auth_starttls' => true, 'ldap_auth_base_dn' => 'ou=People,dc=ldap,dc=mysupercompany,dc=com', 'ldap_auth_user_query' => '(objectclass=inetOrgPerson)', 'ldap_auth_username_attribute' => 'uid', 'ldap_auth_email_attribute' => 'mail', 'ldap_auth_firstname_attribute' => 'givenname', 'ldap_auth_lastname_attribute' => 'sn', 'ldap_auth_fullname_attribute' => 'displayname', 'ldap_auth_isactivedirectory' => false, // ...
A sample configuration for Active Directory is
//'parameters' => array( // ... 'ldap_auth_host' => 'ad.mysupercompany.com', 'ldap_auth_port' => 389, 'ldap_auth_version' => 3, 'ldap_auth_ssl' => false, 'ldap_auth_starttls' => false, 'ldap_auth_base_dn' => 'cn=Users,dc=ad,dc=mysupercompany,dc=com', 'ldap_auth_user_query' => '(objectclass=user)(memberof=marketing)', // careful this can be case sensitive! 'ldap_auth_username_attribute' => 'samaccountname', // this is case sensitive! 'ldap_auth_email_attribute' => 'mail', 'ldap_auth_firstname_attribute' => 'givenname', 'ldap_auth_lastname_attribute' => 'sn', 'ldap_auth_fullname_attribute' => 'displayname', 'ldap_auth_isactivedirectory' => true, 'ldap_auth_activedirectory_domain' => 'ad.mysupercompany.com', // ...
Once the parameters are set, open a new browser and check connection through LDAP. Do not log out until LDAP configuration is valid!
Developments in progress
- Test LDAP Authentication settings
- LDAP bind account and Group management
Contributing
Ideas and suggestions are welcome. Feel free to create an issue or PR on Github using our CONTRIBUTING guidelines.
License
See LICENSE file.