reliforp / reli-prof
A sampling profiler or a memory profiler for PHP written in PHP, which reads information about running PHP VM from outside of the process.
Requires
- php: ^8.4
- ext-ffi: *
- ext-filter: *
- ext-json: *
- ext-pcntl: *
- amphp/amp: 3.1.1
- amphp/parallel: 2.3.3
- hassankhan/config: 3.2.0
- monolog/monolog: 3.10.0
- php-di/php-di: 7.1.1
- sj-i/php-cast: 1.0.0
- symfony/console: ^8.0
- webmozart/assert: 2.3.0
Requires (Dev)
- ext-posix: *
- brianium/paratest: ^7.22
- jetbrains/phpstorm-stubs: 2026.1
- mockery/mockery: 1.6.12
- php-coveralls/php-coveralls: 2.9.1
- phpunit/phpunit: 13.1.7
- psalm/phar: ^6.0
- rector/rector: ^2.4
- squizlabs/php_codesniffer: 4.0.1
Replaces
- 0.13.x-dev
- 0.12.x-dev
- 0.12.0
- 0.11.x-dev
- 0.11.4
- 0.11.3
- 0.11.2
- 0.11.1
- 0.11.0
- 0.10.x-dev
- 0.10.3
- 0.10.2
- 0.10.1
- 0.10.0
- 0.9.x-dev
- 0.9.4
- 0.9.3
- 0.9.2
- 0.9.1
- 0.9.0
- 0.8.x-dev
- 0.8.0
- 0.7.x-dev
- 0.7.0
- 0.6.x-dev
- 0.6.1
- 0.6.0
- 0.5.x-dev
- 0.5.0
- 0.4.2
- 0.4.1
- 0.4.0
- 0.3.8
- 0.3.7
- 0.3.6
- 0.3.5
- 0.3.4
- 0.3.3
- 0.3.2
- 0.3.1
- 0.3.0
- 0.2.1
- 0.2.0
- 0.1.0
- 0.0.9
- 0.0.8
- 0.0.7
- 0.0.6
- 0.0.5
- 0.0.4
- 0.0.3
- 0.0.2
- 0.0.1
- dev-claude/sharp-turing-wXmsm
- dev-claude/investigate-memory-issue-hWlOH
- dev-claude/investigate-memory-issue-NK207
- dev-claude/issue-787-node-labeler-substrate
- dev-claude/issue-787-binary-class-lex-min
- dev-claude/investigate-issue-2408-uKevj
- dev-claude/investigate-snappy-memory-CyRJI
- dev-claude/improve-memory-analysis-FTFtd
- dev-claude/investigate-php-sdk-635-khwQ9
- dev-claude/improve-memory-analysis-K3Bks
- dev-claude/long-running-server-guide-4ZYH2
- dev-claude/phpspy-hybrid-output-option-Kq03T
- dev-claude/test-sqlite-output-PeWhZ
- dev-claude/test-sqlite-memory-23rjL
- dev-claude/unify-memory-output-3Wh8M
- dev-claude/test-sqlite-memory-TziEO
- dev-claude/investigate-file-issue-88-iU3E4
- dev-claude/unprivileged-subprocess-monitoring-GKEk7
- dev-claude/fix-memory-report-oom-71bU1
- dev-claude/investigate-reli-capability-1rocu
- dev-claude/release-notes-0.12.0-draft
- dev-claude/psalm-baseline-rmem-explore-tui
- dev-claude/psalm-baseline-reduction-4
- dev-claude/review-readme-docs-D14yz
- dev-claude/test-ffi-memory-usage-jFoe4
- dev-claude/verify-frankenphp-profiling-docs-sFygi
- dev-claude/debug-arm64-memory-corruption-JoXfw
- dev-claude/verify-frankenphp-arm-bisect-resolver-share-disabled
- dev-claude/improve-memory-report-NKJ41
- dev-claude/ffi-zts-parallel-optimization-V5a0e
- dev-claude/class-table-drop-diag-pT8jW
- dev-claude/investigate-memory-t2-3-SDYVA
- dev-claude/rmem-hover-overlay-X9tPk
- dev-claude/source-location-osc8-2zlQf
- dev-claude/prepare-0.12-release-Up7os
- dev-claude/map-nodes-to-source-KCFbg
- dev-claude/improve-documentation-EucoV
- dev-claude/add-memory-tracking-XcHLO
- dev-claude/analyze-php-memory-issues-dh5ET
- dev-claude/improve-pdo-memory-coverage-SzuI2
- dev-claude/test-reli-memory-analysis-YtwMY
- dev-claude/optimize-memory-analysis-GchbQ
- dev-claude/add-rss-monitoring-MBuvk
- dev-claude/fix-toparrayspass-hang-0bH88
- dev-claude/sqlite-memory-analysis-queries-lfzSo
- dev-claude/fix-memory-dump-analysis-1V8fM
- dev-claude/watch-exec-pid-passing-6S0w2
- dev-claude/add-watch-dump-options-TI5I8
- dev-claude/parallelize-memory-analysis-Pzokm
- dev-claude/add-php-cache-system-4V3Gk
- dev-claude/review-daemon-parallel-processing-h9v6B
- dev-claude/add-xdg-base-directory-gdkq8
- dev-claude/fix-pointedtyperesolver-bug-NTuYT
- dev-claude/propose-features-BMJqm
- dev-claude/improve-memory-analysis-A9gKO
- dev-claude/detect-circular-references-EA0lg
- dev-unloaded-ro-mapping
- dev-fix-zts-detection
- dev-update-issue-template
- dev-backport-fix-doc
- dev-dwarf
- dev-tracing-in-c
- dev-phpcon2020
- dev-experiment-opcode-tracer
This package is auto-updated.
Last update: 2026-05-30 21:16:27 UTC
README
Reli is a sampling profiler (or a VM state inspector) written in PHP. It can read information about a running PHP script from outside the process. It's a standalone CLI tool, so target programs don't need any modifications.
Use it for call-trace sampling (where time is spent), memory-graph analysis (where memory is used), runtime variable inspection, and condition-triggered captures. For first-use, see docs/getting-started.md; for the task map, see the documentation index.
Showcase
A taste of what reli looks like in use.
Sampling with a live hot-frames feed — inspector:trace + watch rbt:analyze
Capture to .rbt in one terminal while running rbt:analyze through watch(1) in another for a live-refreshing "top of the hot frames" view — the data streams in as samples are taken.
# Terminal A — capture (`-f rbt` is implied by the .rbt extension) $ reli inspector:trace -p <pid> -o trace.rbt # Terminal B — live analysis, refreshed every 0.2 seconds $ watch -n0.2 'reli rbt:analyze --last --last-depth=10 --top=10 --sections="tail,self+total" --crop-anchor=right --path=short --crop=auto < trace.rbt'
What you're looking at. reli is a sampling profiler — every ~10 ms it takes a snapshot of the target's PHP call stack. The top pane is what the target is running right now. The self / total tables below rank frames by how many accumulated snapshots they've appeared in: more appearances = more wall time spent there. Self is time directly in the frame; Total is time in the frame plus anything it called.
Compact enough to leave running. At default 10 ms sampling, an hour of trace is rarely more than a few MB of .rbt — capture now, analyse later.
Analyser reference: docs/tracing/rbt-analyze-and-explore.md
Interactive trace browsing — rbt:explore
Capture to .rbt, open the sandwich / flamegraph / tree TUI.
$ reli inspector:trace -p <pid> -o trace.rbt $ reli rbt:explore trace.rbt
Full tour (keymap, filters, --with-opcode, mouse, live tail): docs/tracing/rbt-analyze-and-explore.md
.rbt format spec and converters (speedscope, pprof, callgrind, etc): docs/tracing/binary-trace-format.md
Advanced capture (opcodes / native frames / JIT): docs/tracing/advanced-capture.md
Memory graph visualization — rmem:viz / rmem:explore
Render the heap as a standalone HTML file — Circle Pack, Treemap, Sunburst, 3D Force — or serve it live with a shared focus bus that rmem:explore (TUI), browsers, and an MCP client all follow in sync.
# Recommended for production: short stop, then offline analysis. $ reli inspector:memory:dump -p <pid> -o snapshot.rdump $ reli inspector:memory:analyze snapshot.rdump -f rmem -o snapshot.rmem # Standalone HTML $ reli rmem:viz snapshot.rmem # wrote snapshot.rmem.viz.html # Live (HTTP/SSE) with follow-from-TUI $ reli rmem:explore snapshot.rmem --http-bridge=8080 # press `f` in the TUI, then open http://127.0.0.1:8080/
What you're looking at. reli walks the target's PHP heap into a graph — every value (objects, arrays, strings, call frames…) is a node, every reference is an edge. rmem:viz renders that graph as a standalone HTML page; rmem:explore --http-bridge (or the standalone rmem:live) serves it over HTTP with a shared cursor that the terminal TUI, browser views, and an MCP client all follow at once. Useful for chasing memory leaks and finding which classes eat the most memory.
Full tour (views, palettes, focus bus, mouse, MCP): docs/memory/rmem-explore-and-serve.md
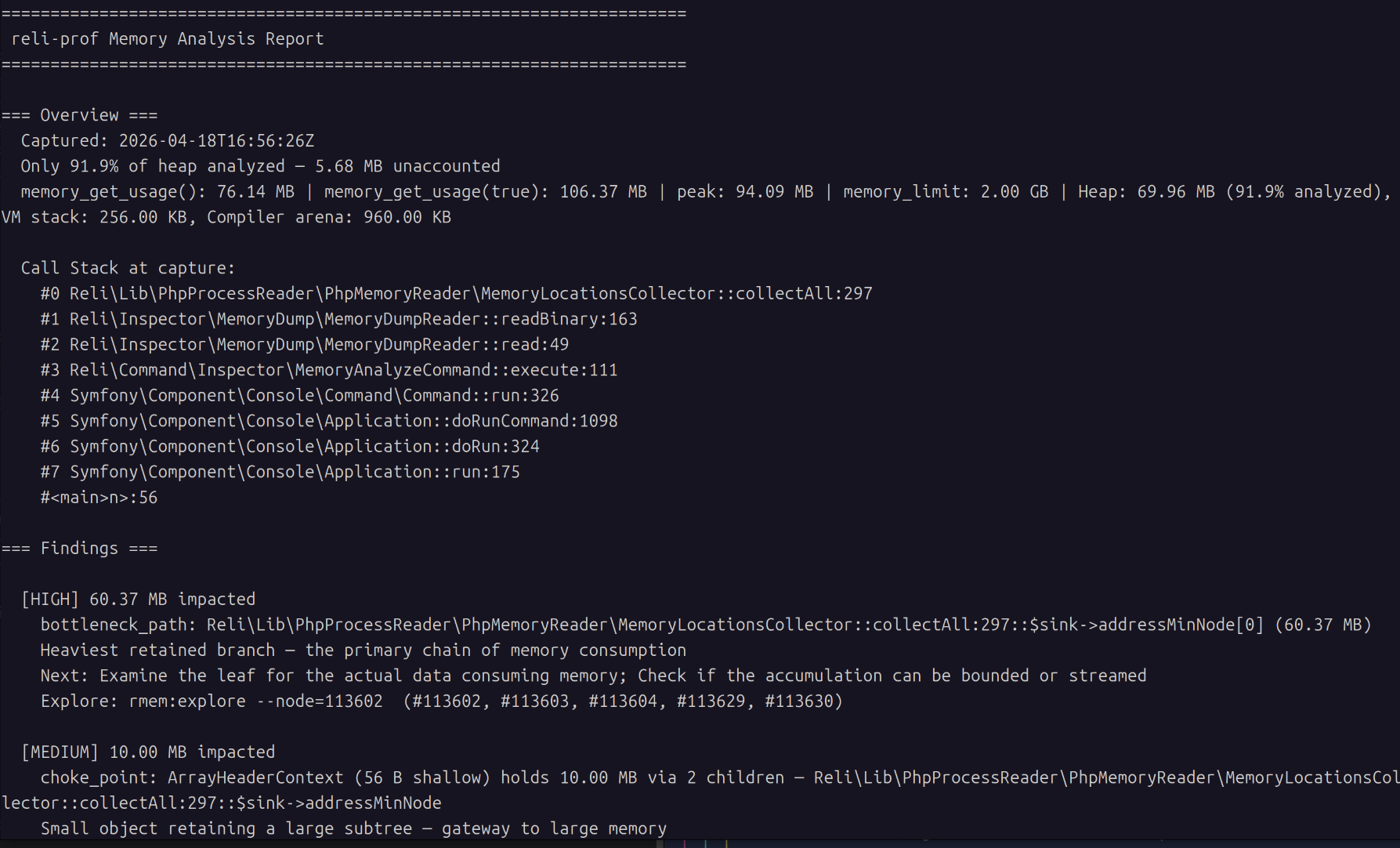
Automated memory findings — inspector:memory:report
Capture a snapshot and get a prioritised report back — dominant classes, cycles, choke points, deduplication candidates — each with severity, hypothesis, and next steps.
# Recommended for production: short stop, then offline analysis. $ reli inspector:memory:dump -p <pid> -o snapshot.rdump $ reli inspector:memory:analyze snapshot.rdump -f rmem -o snapshot.rmem $ reli inspector:memory:report snapshot.rmem
What you're looking at. reli scans the captured heap graph for known waste patterns — dominant classes, reference cycles, choke points, dedup candidates — and prints each finding with a severity, a hypothesis, and a next-investigation step.
You can also compare two snapshots to track regressions or verify fixes:
$ reli inspector:memory:compare before.rmem after.rmem
Full reference (output formats, thresholds, JSON mode): docs/memory/memory-report.md
Capture options (--exclude-heap, portable dumps): docs/memory/memory-dump.md
Core-file analysis (crashed / post-mortem): docs/memory/coredump.md
Troubleshooting
Common hitches (non-standard php binary name, -S for accuracy, Amazon Linux 2 memory maps, stale analysis cache): docs/troubleshooting.md.
How it works
Under the hood, reli:
- Parses the ELF binary of the PHP interpreter.
- Reads the target's memory map from
/proc/<pid>/maps. - Reads memory of the target process through
ptrace(2)andprocess_vm_readv(2)via FFI. - Analyses the internal data structures of the PHP VM (aka Zend Engine).
This keeps target-side overhead low in our benchmarks: 1.00–1.06× baseline at typical sampling rates, with profiler CPU spent in the separate reli process. See docs/bench/RESULTS.md for the numbers.
Goals
We would like to achieve the following 5 goals through this project.
- To be able to closely observe what is happening inside a running PHP script.
- To be a framework for PHP programmers to create a freely customizable PHP profiler.
- To be experimentation for the use of PHP outside of the web, where recent improvements of PHP like JIT and FFI have opened the door.
- Another entry point for PHP programmers to learn about PHP's internal implementation.
- To create a program that remains fun for us to write, even as AI coding agents become part of how we build software.
LICENSE
- MIT (mostly)
- tools/flamegraph/flamegraph.pl is copied from https://github.com/brendangregg/FlameGraph and licenced under the CDDL 1.0. See tools/flamegraph/docs/cddl1.txt and the header of the script.
- Some C headers defining internal structures are extracted from php-src. They are licensed under the Zend Engine License or the PHP License. See src/Lib/PhpInternals/Headers . So here are the words required by the Zend Engine License and the PHP License.
This product includes the Zend Engine, freely available at
http://www.zend.com
This product includes PHP software, freely available from
<http://www.php.net/software/>
What does the name "Reli" mean?
Given its functionality, you might naturally think that the name stands for "Reverse Elephpantineer's Lovable Infrastructure". But unfortunately, it's not true.
"Reli" means nothing, though you are free to think of this tool as something reliable, religious, relishable, or whatever other reli-s you like.
Initially, the name of this tool was just "php-profiler". Due to a licensing problem (#175), this perfectly good name had to be changed.
So we applied a randomly chosen string manipulation function to the original name. strrev('php-profiler') results in 'reliforp-php', and it can be read as "reli for p(php)".
Thus, the name of this tool is "Reli for PH*" now. And you can also just call it "Reli".
See also
- adsr/phpspy — Reli is heavily inspired by phpspy. For how the two differ and when to reach for which, see docs/comparison.md.